Windows WebDAV flaw fuels stealth malware spread
Threat actors are exploiting a legacy Windows feature to deliver remote access malware while sidestepping conventional browser safeguards and some endpoint monitoring tools, according to new findings from cybersecurity researchers. Investigators at Cofense Intelligence have identified an ongoing campaign in which attackers abuse the Web Distributed Authoring and Versioning protocol, known as WebDAV, in combination with Windows File Explorer. The technique allows malicious files hosted on remote […] The article Windows WebDAV flaw fuels stealth malware spread appeared first on Arabian Post.
Threat actors are exploiting a legacy Windows feature to deliver remote access malware while sidestepping conventional browser safeguards and some endpoint monitoring tools, according to new findings from cybersecurity researchers.
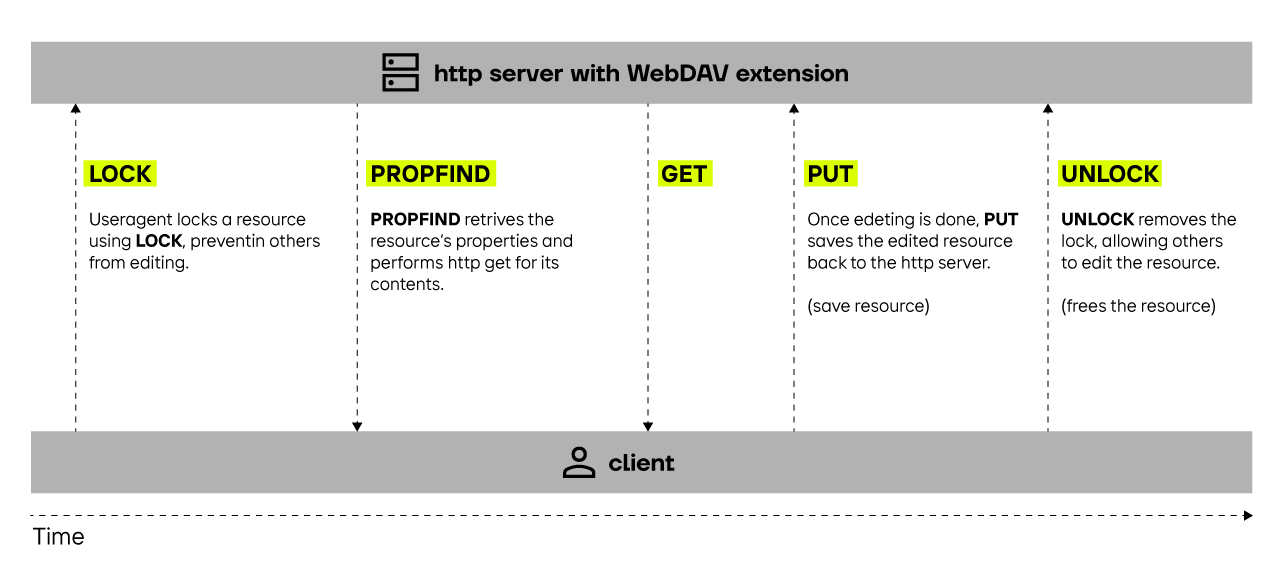
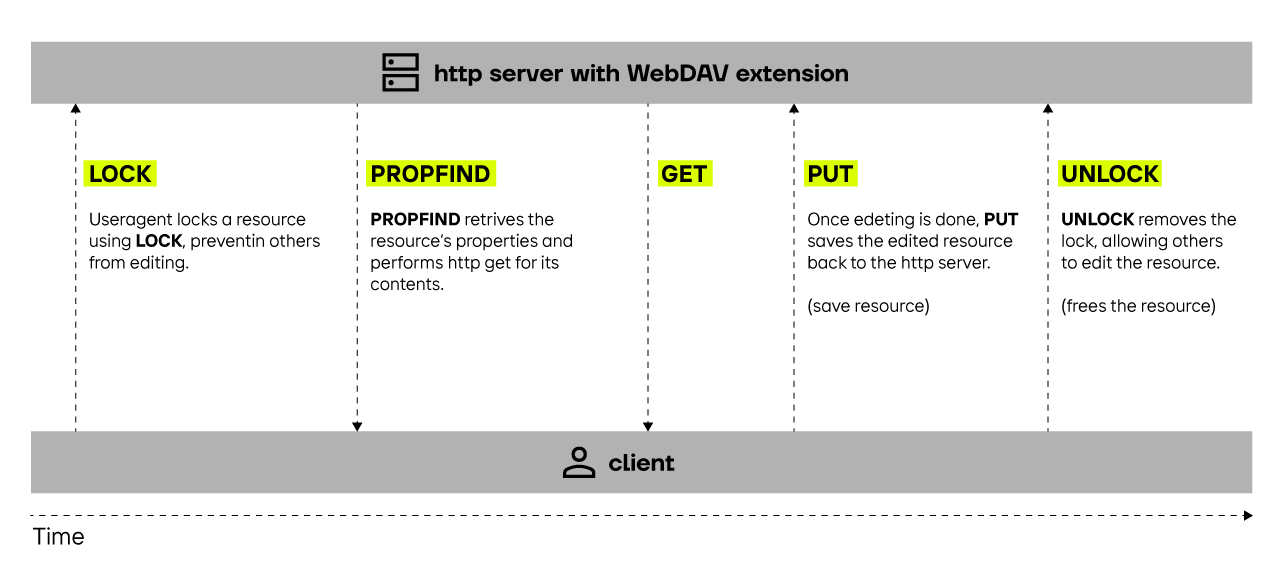
Investigators at Cofense Intelligence have identified an ongoing campaign in which attackers abuse the Web Distributed Authoring and Versioning protocol, known as WebDAV, in combination with Windows File Explorer. The technique allows malicious files hosted on remote servers to be accessed and executed through the operating system’s native file management interface, rather than via a web browser, reducing the likelihood of detection by traditional web security controls.
WebDAV is an extension of the HTTP protocol that enables users to manage files on remote web servers as if they were stored locally. Although developed in the late 1990s to facilitate collaborative editing and file sharing over the internet, it remains supported in modern versions of Microsoft Windows, including Windows 10 and Windows 11. Its integration into File Explorer permits remote folders to be mounted and browsed directly within the desktop environment.
Security researchers say attackers are capitalising on this functionality by sending phishing emails that contain links formatted to open through File Explorer using the “file://” or WebDAV paths. When recipients click the link, the system connects to a remote WebDAV server controlled by the threat actor. Victims are then presented with what appears to be a standard file directory, often containing a shortcut or document icon designed to resemble a legitimate file.
Once opened, these files trigger the download and execution of a Remote Access Trojan, or RAT, granting attackers persistent access to the compromised system. RATs typically allow threat actors to exfiltrate data, capture keystrokes, deploy additional payloads, and move laterally across networks. In corporate environments, this can lead to credential theft, ransomware deployment or broader network compromise.
Cofense Intelligence analysts note that because the interaction occurs through Windows File Explorer rather than a browser session, certain security layers may not be activated. Web browsers commonly include sandboxing, URL filtering, and reputation-based blocking mechanisms. By contrast, File Explorer connections to WebDAV shares may not trigger the same scrutiny, particularly in environments where legacy protocols remain enabled for compatibility reasons.
Cybersecurity specialists have long warned about the risks associated with legacy services embedded within operating systems. WebDAV has featured in multiple attack chains over the past decade, often in conjunction with phishing campaigns. Microsoft has issued guidance over the years advising administrators to disable WebClient services linked to WebDAV where not required, but many organisations continue to rely on them for internal workflows or legacy applications.
The latest campaign reflects a broader trend in which threat actors seek to bypass endpoint detection and response systems by abusing trusted, built-in tools. This approach, often referred to as “living off the land”, reduces the need to introduce clearly malicious binaries at the initial stage of compromise. Instead, attackers exploit legitimate system components to establish a foothold before deploying more overt malware.
Security firms tracking phishing activity report a sustained increase in email-based intrusion attempts targeting both enterprises and public sector entities. Attackers frequently impersonate financial institutions, logistics companies or internal departments, crafting messages that create a sense of urgency. By embedding WebDAV paths in hyperlinks or disguised buttons, they can initiate connections that appear routine to the end user.
Experts caution that while some endpoint detection platforms can identify anomalous network connections or suspicious child processes spawned by File Explorer, detection is not universal. Systems that rely heavily on browser-based inspection or gateway filtering may overlook activity initiated through native operating system protocols.
The emergence of this campaign coincides with heightened scrutiny of supply chain vulnerabilities and remote access tools. Over the past year, several high-profile breaches have involved attackers leveraging legitimate administrative utilities to maintain persistence. Analysts say the WebDAV technique underscores how older technologies, when left enabled by default, can be repurposed in modern attack scenarios.
Mitigation strategies recommended by cybersecurity professionals include disabling the WebClient service if WebDAV is not essential, restricting outbound connections to untrusted WebDAV servers, and ensuring that endpoint monitoring solutions are configured to flag suspicious behaviour originating from File Explorer. User awareness training also remains a critical defence, as phishing emails serve as the primary delivery vector.
Microsoft has not announced any specific vulnerability related to WebDAV in this context, as the abuse hinges on legitimate functionality rather than a coding flaw. Nonetheless, enterprise administrators are encouraged to review system configurations and apply the principle of least privilege to minimise exposure.
The article Windows WebDAV flaw fuels stealth malware spread appeared first on Arabian Post.
What's Your Reaction?